I stumbled across this while trouble shooting a problem with GPO’s in Windows Server 2016. My GPO’s we stopping half way through applying because there was a n error. There was an error in the RSOP, with a surprising amount of detail on how to correct it, only that all the documentation was wrong or outdated. The error was like below (for word searches).
Anyway, when I tried running the commands, I found two things, winlogon.log did not exist anymore, and that the secedit command was also old. Best following ‘askpfeplat’ blog below, I add the special notes that;
- The registry switch needs to be set to ‘2’ (He is showing how it should be)
- Gpupdate /force will now work in Server 2016
- In my experience, I did not need a server reboot to apply the settings
Hope this saves someone else some time.
- References
- https://support.microsoft.com/en-us/help/324383/troubleshooting-scecli-1202-events
- https://blogs.technet.microsoft.com/askpfeplat/2017/04/18/hey-dude-wheres-my-winlogon-log/
Log Name: Application
Source: SceCli
Date: 08.03.2017 17:49:21
Event ID: 1202
Task Category: None
Level: Warning
Keywords: Classic
User: N/A
Computer: test2016.mydomain.com
Description:
Security policies were propagated with warning. 0x534 : No mapping between account names and security IDs was done.
Advanced help for this problem is available on http://support.microsoft.com. Query for “troubleshooting 1202 events”.
Error 0x534 occurs when a user account in one or more Group Policy objects (GPOs) could not be resolved to a SID. This error is possibly caused by a mistyped or deleted user account referenced in either the User Rights or Restricted Groups branch of a GPO. To resolve this event, contact an administrator in the domain to perform the following actions:
-
Identify accounts that could not be resolved to a SID:
- From the command prompt, type: FIND /I “Cannot find” %SYSTEMROOT%\Security\Logs\winlogon.log
- The string following “Cannot find” in the FIND output identifies the problem account names.
- Example: Cannot find JohnDough.
- In this case, the SID for username “JohnDough” could not be determined. This most likely occurs because the account was deleted, renamed, or is spelled differently (e.g. “JohnDoe”).
-
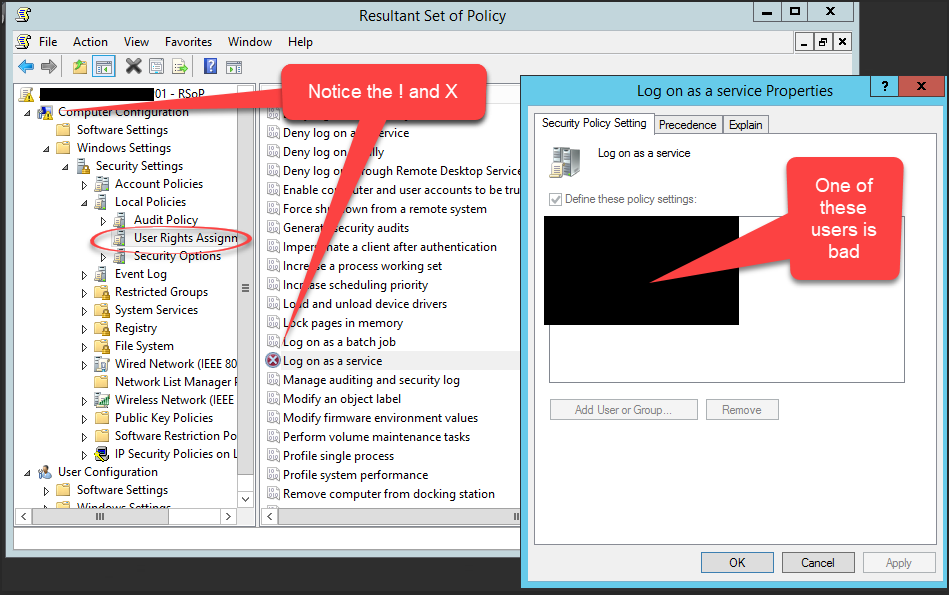
Use RSoP to identify the specific User Rights, Restricted Groups, and Source GPOs that contain the problem accounts:
- Start -> Run -> RSoP.msc
- Review the results for Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment and Computer Configuration\Windows Settings\Security Settings\Local Policies\Restricted Groups for any errors flagged with a red X.
- For any User Right or Restricted Group marked with a red X, the corresponding GPO that contains the problem policy setting is listed under the column entitled “Source GPO”. Note the specific User Rights, Restricted Groups and containing Source GPOs that are generating errors.
-
Remove unresolved accounts from Group Policy
- Start -> Run -> MMC.EXE
- From the File menu select “Add/Remove Snap-in…”
- From the “Add/Remove Snap-in” dialog box select “Add…”
- In the “Add Standalone Snap-in” dialog box select “Group Policy” and click “Add”
- In the “Select Group Policy Object” dialog box click the “Browse” button.
- On the “Browse for a Group Policy Object” dialog box choose the “All” tab
- For each source GPO identified in step 2, correct the specific User Rights or Restricted Groups that were flagged with a red X in step 2. These User Rights or Restricted Groups can be corrected by removing or correcting any references to the problem accounts that were identified in step 1.